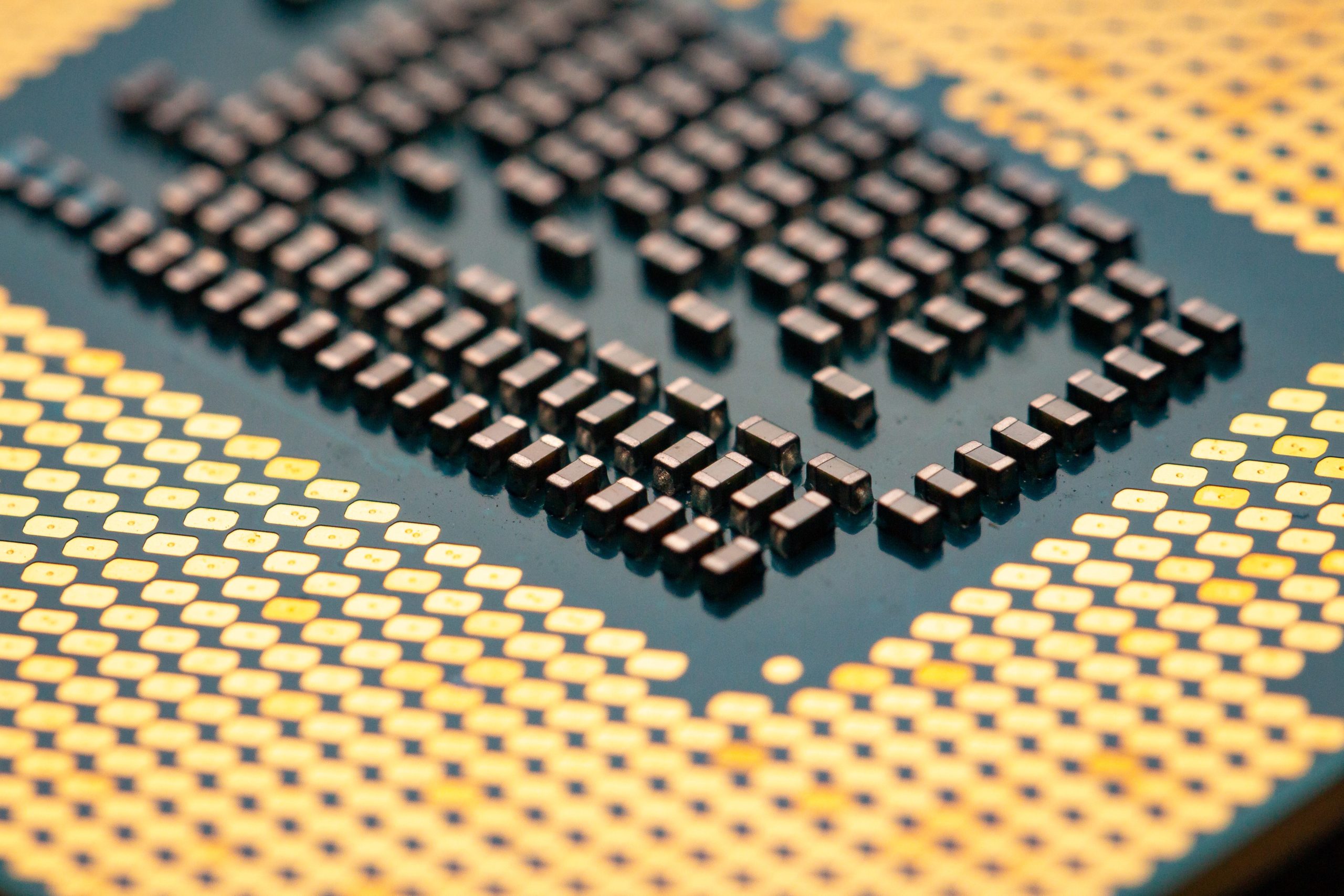
In the modern digital age, computer security has become a critical concern. With sensitive information being stored and transmitted online, it is more important than ever to ensure that our data and devices are protected against malicious attacks. The RISCoT project aims to do just that. By leveraging the power of RISC-V architecture and trusted execution environments (TEEs), the RISCoT project is creating a new era in secure computing.
In this blog post, we’ll take a closer look at what the RISCoT project is and what I achieved after 1.5 years of research. So, keep reading to learn more!
What is RISCoT?

In the RISCoT project, which started in February 2021 and finished in August 2022, I took on the role of lead researcher and team manager, diving deep into the world of Trusted Execution Environments (TEEs) on RISC-V architecture. Throughout the course of the project, I conducted extensive research on the security of TEEs on RISC-V, leveraging my knowledge and experience to further advance the field. I was also responsible for managing a talented team of three software engineers, who worked under my supervision to develop various software tools that are now available to the research community.
Did you know? RISCoT stands for “RISC(-V) of Trustâ€, a play-on-words of RISC-V, Trusted Environments and IoT.
A TEE is a processor feature that isolates some special apps from the general system. It is a pretty niche research field, but TEEs are widely used in smartphones, which is why they are interesting to explore, break and fix. RISC-V on the other side is a relatively new architecture, so there is not that much research about it.
Results
The hard work and dedication paid off as I successfully wrote and had accepted at least one research paper (with another one on the way to submission) on the topic. This was a major accomplishment and a testament to the impact of our work in the field.
In order to counter the challenges posed by the ongoing pandemic, I was able to create a virtual lab environment that allowed my team and I to continue our research, do experiments on hardware and more.
I hope to write more about managing and leading this project in the next few months, so stay tuned!
Be First to Comment