A few years ago, I made a blog post about a technique called “tab nabbingâ€, which can be used to trick the user into entering their data into a phishing website. The post with the really SEO1-unfriendly name can be found here:
The vulnerability is that, linking to resources gives these resources full control over the original window. Therefore, a malicious website can “nab†the tab and call a different website or show new elements on the caller tab, such as fake login screens. Website owners could only prevent this by adding rel="noopener" to links that use target="_blank". At the time this was not really a doable solution, as every website would have needed to do this for all links.
I revisited my own blog, and if you try it now, nothing special will happen. The reason for this is that browser now automatically add the above tag to all “target blank†links. And this was implemented as an opt-out feature. All major browsers implemented this.
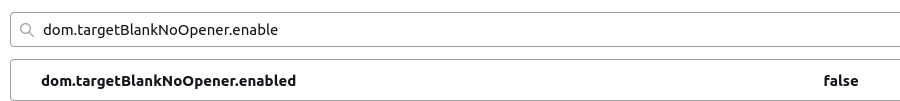
You can make the “vulnerability†work again on Firefox only, as it allows disabling the protection. In Firefox, enter about:config into the URL bar, confirm, then put the following into the search bar: dom.targetBlankNoOpener.enabled.
Double-Click the resulting entry and it should say false.
Please remember to change it back and re-enable the protection after experimenting!
Photo by Choong Deng Xiang on Unsplash
- Search Engine Optimization ↩︎

Be First to Comment